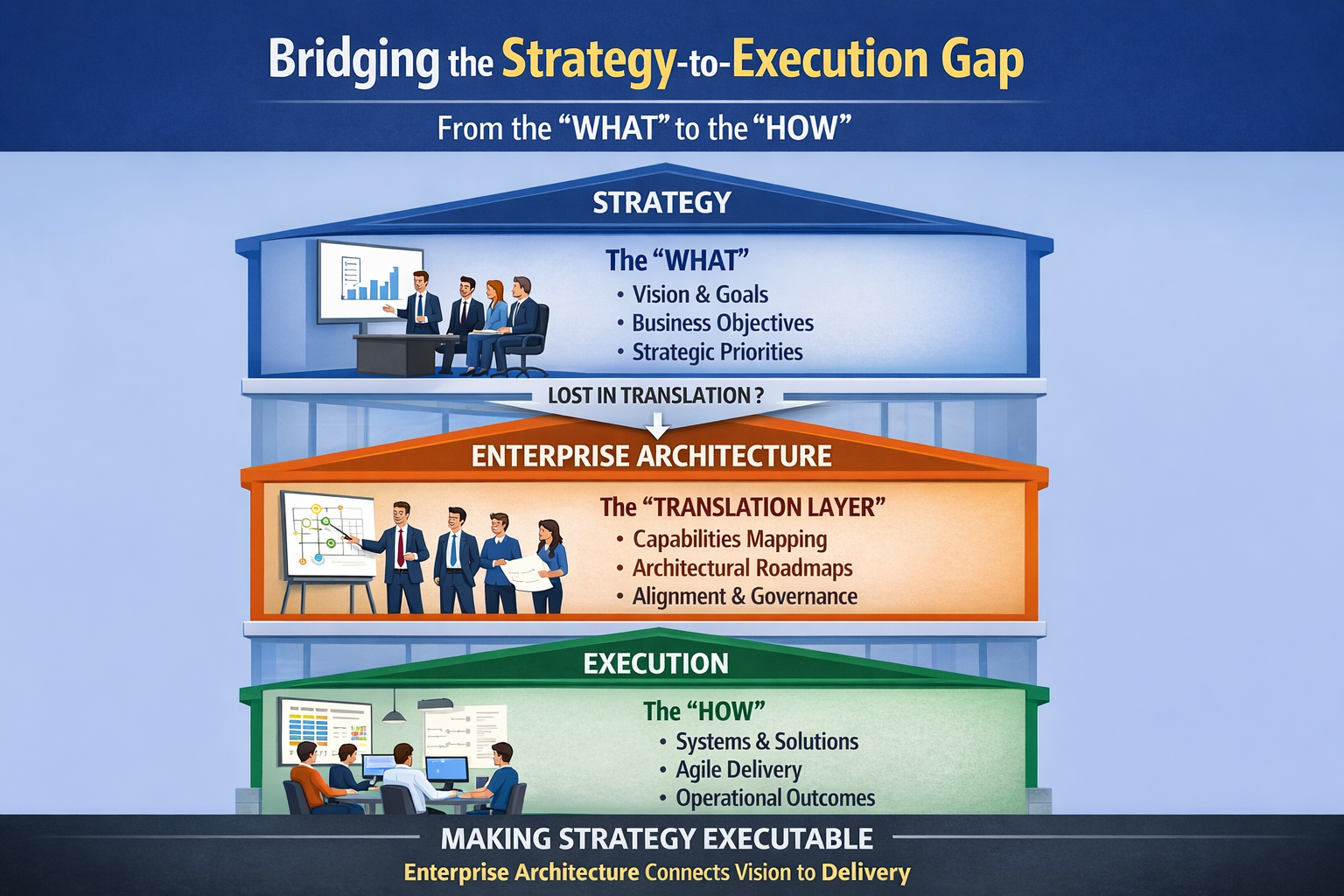
Executive Summary
- Who this is for: Enterprise Architects, Solution Architects, Architecture Leads, Domain-Driven Design practitioners
- Problem it solves: Governance gaps — missing owners, conflicting authorities, undecided policies — stay invisible until production fails
- Key outcome: A structured second Event Storming pass that turns a domain model into a governance gap register
- Time to implement: 30–60 days to run both passes and act on findings
- Business impact: Earlier visibility of ownership conflicts, reduced production surprises, and governance decisions made in workshops instead of postmortems
The Fire Marshal and the Architect
Imagine a large office building.
An architect visits to understand the layout.
They map the floors.
They document the rooms.
They record how people move through the space.
They leave with a complete picture of the building's structure.
Then the fire marshal visits.
Same building. Same floors. Same rooms.
But the fire marshal is not mapping the building.
They are asking a completely different set of questions.
Who holds the key to this room?
Who decided this stairwell would stay locked?
What happens if this corridor fills with smoke and nobody has authority to open that door?
The architect produced an accurate map.
The fire marshal found every decision that was never made.
Both visited the same building.
Neither saw what the other saw.
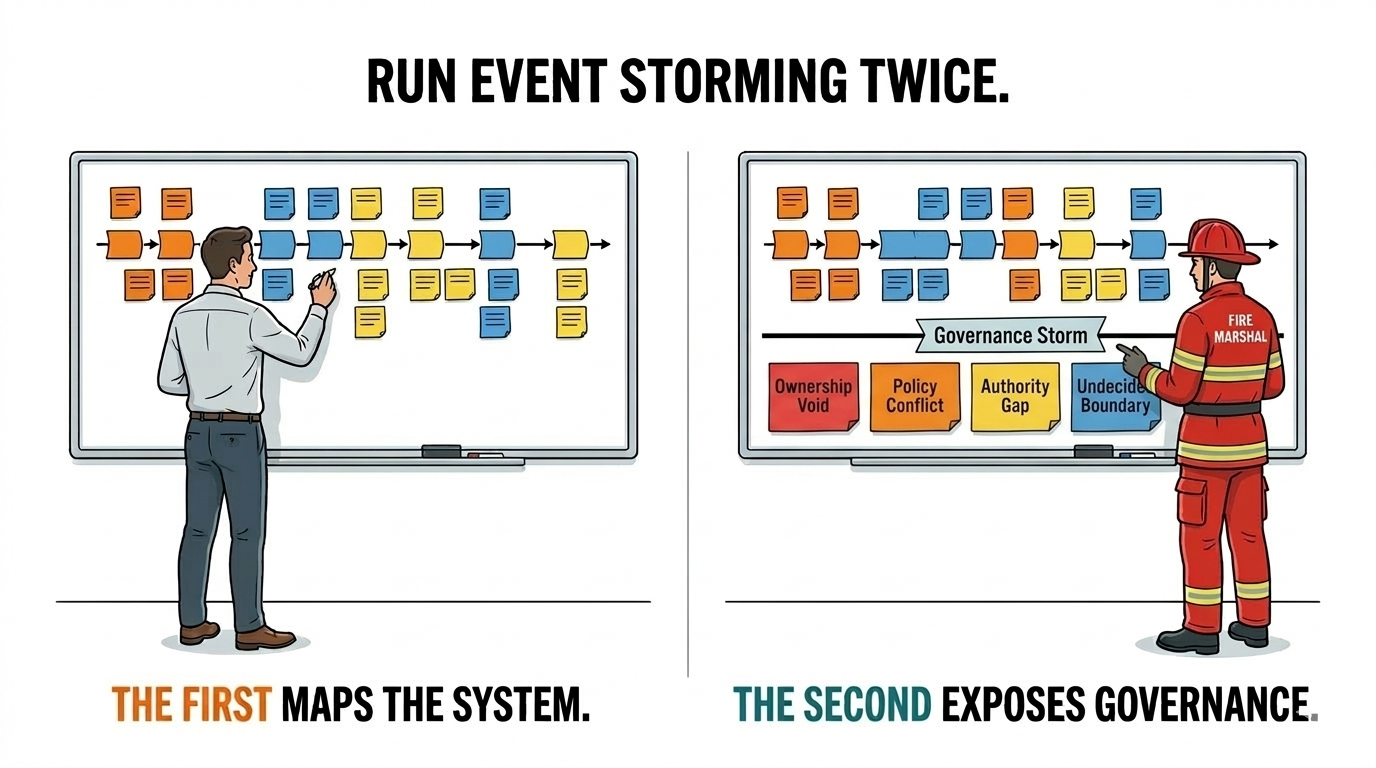
This is exactly what happens in most Event Storming workshops.
The Workshop That Stops Too Soon
Event Storming is one of the most powerful tools in an architect's practice.
A room full of stakeholders.
Sticky notes on a wall.
Domain events in orange. Commands in blue. Aggregates in yellow.
In a few hours, a team can map a complex domain that would take weeks to document conventionally.
The output is genuine.
The domain becomes visible.
Boundaries emerge.
Hotspots surface.
And then the workshop ends.
The sticky notes get photographed.
The model goes into Confluence.
And the governance gaps — the missing owners, the conflicting authorities, the undecided policies — stay exactly where they were.
Invisible.
What the First Pass Does Not See
The first Event Storming pass answers one question very well.
What does the system do?
It does not answer the questions that governance depends on.
Who has authority to trigger this command?
What policy governs this decision — and who owns that policy?
When this event fires and two systems react simultaneously, who decides which response takes precedence?
Who is accountable when this aggregate behaves in a way nobody intended?
These are not domain questions.
They are governance questions.
And they are hiding in plain sight on the same wall where the domain model lives.
The first pass maps every room in the building.
The governance gaps are the unmarked exits.
They do not appear until someone looks for them deliberately.
The Governance Storm
The second pass has a name.
Governance Storm (GS).
Governance Storm is a structured second Event Storming session applied to an existing domain model.
Its purpose is not to refine the domain.
Its purpose is to interrogate the governance layer beneath it.
In a Governance Storm, the same timeline remains on the wall.
But a second layer of sticky notes appears beneath it.
For every command, one question: Who has authority to issue this — and is that documented?
For every policy, one question: Who owns this policy — and what happens when it conflicts with another?
For every hotspot, one question: Is this a domain complexity or a governance gap?
The bottom row will always be longer than the top.
The Governance Storm Model
A Governance Storm session operates with four signal types.
Each maps to a governance gap category.
Signal 1: Ownership Void
An event fires. A command gets issued. An aggregate changes state.
But when the workshop asks who owns this — silence.
Multiple people look at each other.
Nobody claims it.
Or three people claim it simultaneously and cannot agree.
This is an Ownership Void.
It is not a domain problem.
It is an accountability structure that was never designed.
Signal 2: Policy Conflict
Two policies exist for the same decision point.
They were written by different teams.
Neither team knows the other's policy exists.
When the same event fires, both policies activate.
The system has no instruction for which one wins.
This is a Policy Conflict.
It lives silently in the model until a transaction exposes it.
Signal 3: Authority Gap
A command exists with no defined authority.
Anyone can issue it.
Or nobody can — because no team has claimed the right to trigger it.
This is an Authority Gap.
It is different from an Ownership Void.
The capability exists. The authority to invoke it does not.
Signal 4: Undecided Boundary
Two bounded contexts share a concept.
Neither team is willing to own it entirely.
Neither team is willing to give it up.
The boundary sits in the model, unresolved.
Every integration across that boundary carries the cost of that unresolved decision.
This is an Undecided Boundary.
It will generate incidents until someone makes the boundary decision.
The Two-Row Map
The output of a Governance Storm is a two-row sticky-note map.
Top row: The domain model from the first Event Storming pass.
Events. Commands. Aggregates. Policies.
Bottom row: The governance layer exposed by the second pass.
Ownership Voids. Policy Conflicts. Authority Gaps. Undecided Boundaries.
The bottom row will always be longer than the top.
Not because the team failed.
Because governance gaps accumulate invisibly until someone looks.
| Domain Layer (Top Row) | Governance Layer (Bottom Row) |
|---|---|
| OrderPlaced event | No defined owner for order validation policy |
| ProcessPayment command | Authority gap — three teams claim the right to trigger |
| FraudDetected event | Policy conflict — risk team and compliance team have different responses |
| Customer boundary | Undecided — shared between commerce and CRM domains |
| ShipmentDispatched event | Ownership void — logistics owns the event, nobody owns the failure path |
Every row in the bottom layer is a governance finding.
Every finding that goes unaddressed becomes a production incident.
What Breaks When the Second Pass Never Happens
When teams run only one Event Storming pass:
Ownership conflicts survive into production.
Two teams both believe they own the same command.
The conflict stays invisible until a live incident forces a decision — under pressure, with real consequences.
Policy gaps become architectural debt.
A policy that was never owned gets implemented differently in three services.
The divergence grows quietly.
By the time it surfaces, unwinding it requires a cross-team programme, not a workshop.
Boundary disputes generate permanent integration tax.
An undecided boundary does not resolve itself.
It generates repeated integration meetings, repeated negotiations, and repeated incidents — until someone makes the decision that the original workshop could have surfaced in twenty minutes.
When the Governance Storm is run:
Ownership conflicts are found in the workshop.
Not in the postmortem.
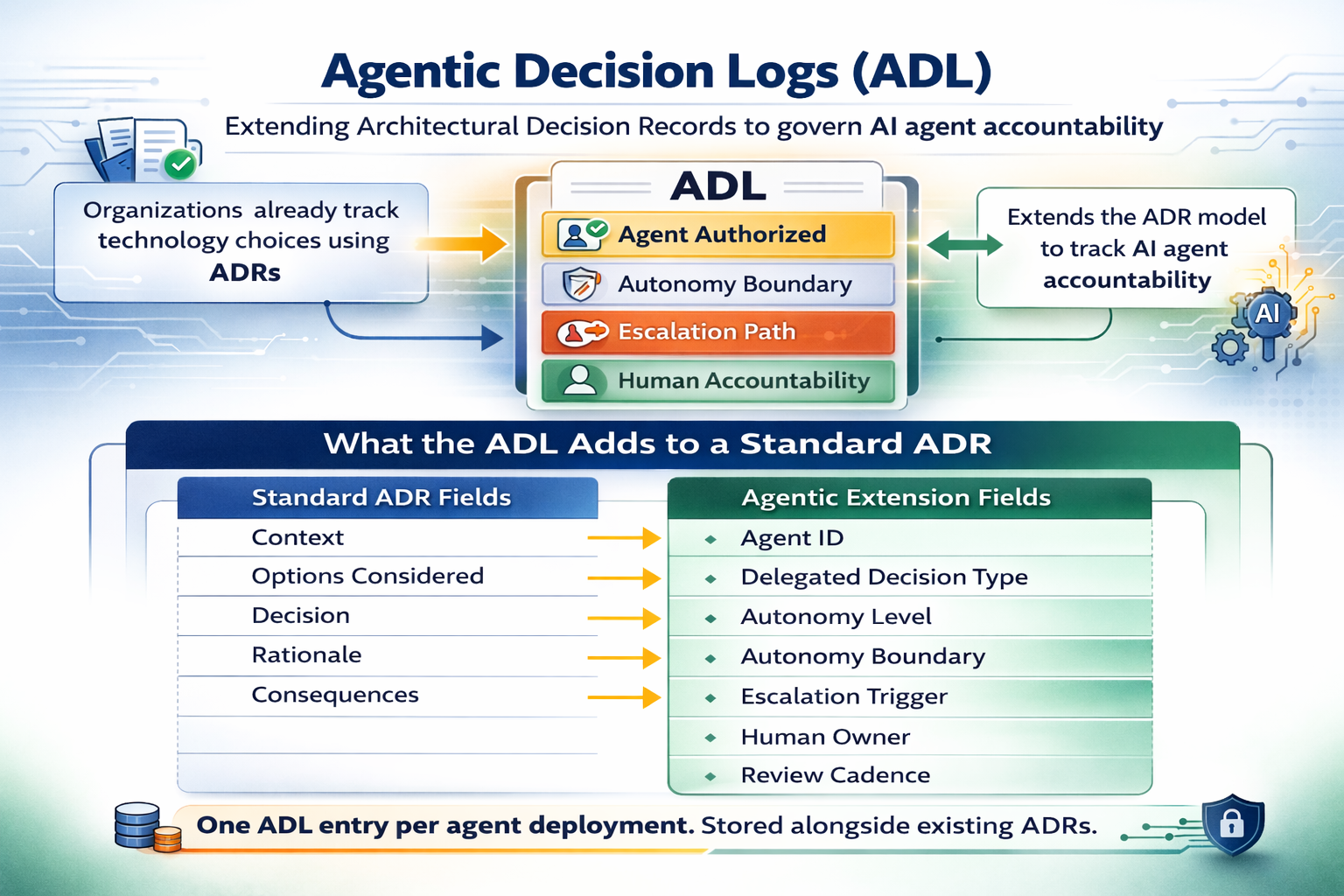
Policy gaps become ADR candidates immediately.
Boundary decisions get made before they become structural debt.
The building gets its fire exits labeled before the fire.
Implementation Guide (30–60 Days)
Introducing Governance Storm requires discipline more than technology.
The sticky notes are the same.
The questions are different.
Run a standard Event Storming session on the target domain.
Map domain events, commands, aggregates, and policies.
Identify hotspots in the usual way.
Do not attempt governance interrogation in this session.
The first pass must be complete before the second begins.
Deliverable: Complete domain model for the target bounded context
Success Metric: All domain events documented with clear commands and aggregates. At least three hotspots identified.
Phase 2: Run the Governance Storm (Weeks 3–4)
Reconvene the workshop — ideally within one week of the first pass.
Keep the original model on the wall.
Introduce the four Governance Storm signal cards:
- Ownership Void
- Policy Conflict
- Authority Gap
- Undecided Boundary
For every event and command, ask the four governance questions.
Map findings on the bottom row using the signal card colors.
Deliverable: Two-row model with full governance layer populated. Governance findings documented per domain event.
Success Metric: At least one Ownership Void, one Policy Conflict, and one Authority Gap identified and documented. Each finding assigned an owner and a resolution action.
Phase 3: Convert Findings to Governance Actions (Weeks 5–8)
For each Governance Storm finding, assign one of three dispositions:
Resolve now: Ownership Voids and Authority Gaps that can be closed within 30 days. Assign to named owner. Document as ADR.
Escalate: Policy Conflicts and Undecided Boundaries that require cross-team or leadership decisions. Assign to Architecture Review Board with a time-bounded resolution date.
Accept and document: Governance gaps that are known, understood, and acceptable to carry. Document explicitly as a recognized architecture risk.
Deliverable: Governance finding register with disposition, owner, and resolution timeline per finding
Success Metric: All findings dispositioned. At least two resolved as formal ADRs within the 30-day window.
Evidence from Practice
Organizations that run Governance Storm for the first time consistently find the same thing.
The Ownership Void count is higher than anyone expected.
Not because the teams are disorganized.
Because ownership was assumed during system design and never formally assigned.
Assumed ownership holds until the first cross-team dependency makes the assumption visible.
That visibility usually arrives as a production incident.
The Policy Conflict findings produce a different kind of discomfort.
Teams discover they have been running parallel policies for the same decision for months.
Neither team knew.
Both assumed consistency.
The divergence had been accumulating silently in their separate backlogs.
The Undecided Boundaries produce the most important conversations.
Boundaries that architects have been gently avoiding — because the ownership conversation is difficult — finally get named.
Named as a governance gap, not as a political problem.
That reframe changes the conversation completely.
Action Plan
This Week
Ask three questions:
- In your last Event Storming session — did you identify who has authority over each command, or only what the command does?
- Can you name the owner of every policy currently mapped in your domain model?
- How many of your domain hotspots are actually governance gaps that were never resolved?
If these answers are unclear, the second pass has never been run.
Next 30 Days
Select one bounded context.
Run a standard first-pass Event Storming session if one does not already exist.
Schedule the Governance Storm within one week.
Use the four signal types.
Build the two-row map.
Document every finding.
3–6 Months
Embed Governance Storm as a standard second step in all Event Storming programs.
Make it a prerequisite for architecture review of any new domain.
Integrate governance findings into the ADR pipeline as standard inputs.
Governance decisions made in workshops do not become production incidents.
Final Thought
The architect mapped every room.
The fire marshal found every unmarked exit.
Same building.
Completely different questions.
The first Event Storm shows what the system does.
The second one shows who is responsible for it — and where nobody is.
Turn Your Next Event Storming Session Into a Governance Intelligence Exercise
If your Event Storming workshops produce domain models but never surface ownership gaps…
if governance conflicts only become visible when delivery has already stalled…
or if policy decisions are still being made in incident retrospectives rather than design sessions —
your organization may be stopping one pass too early.
In a focused 30-minute Governance Storm Diagnostic, we will:
- Evaluate whether your current Event Storming practice surfaces governance signals
- Identify Ownership Voids, Policy Conflicts, and Authority Gaps in your current domain model
- Introduce the Governance Storm model for your architecture practice
- Define a 30-day plan to run both passes on your highest-priority bounded context
No complex tooling.
No governance theater.
No ownership conversations postponed until production forces them.
Just a second pass that finds what the first one was never designed to look for.
→ Book an Architecture Strategy Session
or
The first Event Storm maps the system.
The second one reveals who owns nothing.